April 2025
The Persian Gulf remains the node of energy and political tensions, but in recent years, the geopolitical pressure has been more clearly being transported into the digital space. Countries of the region are nowadays protecting their systems as they are protecting energy networks under voltage, since each mistake reveals a crack in the encryption of power. Attacks against the infrastructure are becoming a part of the algorithmic politics and are thus forming security calculations equally strong as any rocket or diplomatic incident.
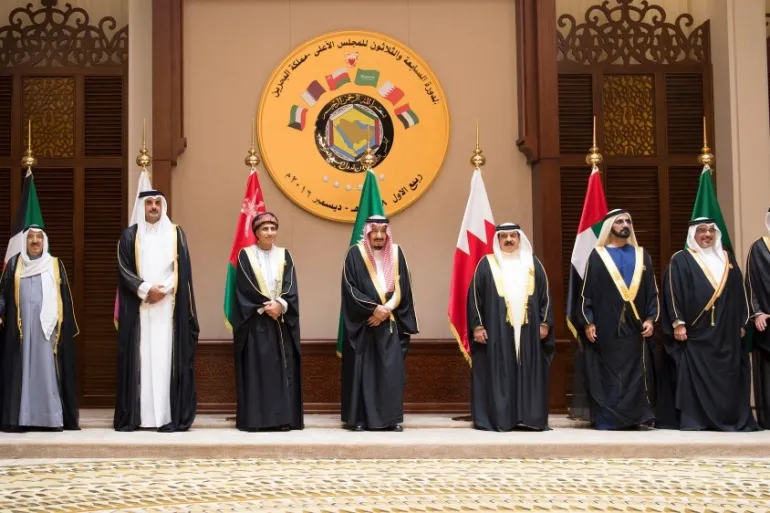
The Gulf Cooperation Council (GCC) countries are thus constructing their digital sovereignty fast. They are no longer perceiving cybersecurity solely as a technical sector, but nowadays perceive it as a central pillar of political stability. Each attack impacts the perception of state resilience, especially regarding its relations with Iran, the US, China, and Israel. In such an environment, vulnerabilities are not solely holes in the code; they are strategic points of pressure.
Iran is developing an advance cyber network. It combines offensive groups, propaganda operations, and hybrid campaigns that target energy and financial systems throughout the Gulf. These attacks do not produce long-term disruptions, but do create a destabilizing effect. They act as a low-intensity response to regional pressures. Examples from Saudi Arabia, Qatar, and the UAE show that Tehran is using the digital space as its own system of retaliatory “parameter setting”, strong enough to raise tensions, but not to cause a direct war.
The Gulf states see that the traditional security architecture cannot cover digital risks anymore. That is why they are introducing new institutions. Saudi Arabia is strengthening the new National Cyber Security Authority. The UAE is developing the Cyber Security Council. Qaar is integrating military and financial systems into a unique fusion center. Each of these structures functions as a node in the wider regional system, but the links between these nodes are still not stable. The lack of a common protocol on the GCC level is making coordination difficult. Smaller countries worry that centralization would endanger their digital sovereignty.
The United States of America is attempting to strengthen regional integration through early detection systems. However, their suggestions face resistance due to data sensitivity. At the same time, the engineering competition between Washington and Beijing is transferred to the Gulf infrastructure. The Gulf countries are increasingly often using the Chinese cloud services and AI systems, which leads them straight into a parallel technological ecosystem. For them, China is a partner that does not set political conditions, but such a relationship opens up the issue of technological dependence.
Israel is offering advanced security systems. The countries of the region are accepting them, but are still combining them with American standards and Chinese equipment. Thus, they are creating hybrid networks that function as complex digital mechanisms. But hybridization is increasing the risk. Each inconsistency can become a security omission.
By 2025, it will have become clear that the Gulf countries treat the digital domain as a strategic field that requires control of the cloud infrastructure, data, and AI systems. NEOM and similar projects are gaining the function of a test-polygon for the “sovereign Internet” models. In parallel, domestic hubs and training centers are improved. New laws resemble the European GDPR, but leave more space to state organs.
The main causes remain clear. The first one is regional coordination, without which each state must defend its own networks in isolation. The second one is the problem of dependence on external providers who can limit digital sovereignty. The third is depicted in the balance between security and internal control, because stronger monitoring often weakens the space for innovations.
If the countries of the region link digital defense with a wider concept of resilience, they could create a stable technological corridor in the Global South. Contrary to that, their cyberspace becomes the line of division of grand powers, where data, protocols, and codes will replace the traditional instruments of power.
Author: Aleksandar Stanković